 Are you doing all you can to keep hackers out of your house?
Are you doing all you can to keep hackers out of your house?
We all know that smart appliances like televisions, refrigerators, thermostats and the many other systems that are controlled from our smart phones offer many benefits to our busy lives. But they also present some very real risks if not managed. As the number of us using home networks for these applications rises, so does the risk of cyber attacks. Most of these devices carry easily-hacked default codes and password which, when used right out-of-the-box, can expose your IP address to the internet where hackers can find it.
What does a cyber invasion look like?
Once they have access, these thieves will breach your home network security. If this happens, they can use your personal and financial information. Moreover, they can hijack your devices and extort high-dollar ransoms from you for computer files held hostage. They can even control your appliances – perhaps setting the temperature all the way up via your smart thermostat on the hottest day of the year and not releasing it until you pay the ransom. Often however, these criminals will continue to use your network for their own purposes without you even knowing it.
Can you avoid these cyber attacks?
There are steps you can take and habits you can adopt to help keep your home network safe from hackers. Here are tips from the experts to secure your devices. Here are 10 tips to help homeowners keep their home systems safe:
Software Updates: don’t ignore the latest updates and security patches that become available for phones, appliances and other electronics. Often, they include “fixes” for security vulnerabilities that have been discovered since the device was sold.
Password Authentication: Whenever possible, take advantage of two-factor authentication offered by many financial institutions. A code (usually only valid for a matter of minutes) is sent via a separate text or e-mail to be used along with a password during log-in. If a hacker is monitoring your device, they will not have access to the separate code and thus cannot gain access to the account you are opening.
Network Security: Treat your home network as you would your business office network. Prevent unauthorized access by changing default settings, user names and passwords when devices are installed and periodically thereafter. When installing new devices, use a firewall rather than a link through another device. Take the time to see that your passwords are complex – not easily guessed.
Bluetooth Device: If your network has any vulnerability, hackers can exploit your Bluetooth function to listen in or gain access to other connected devices. Turn off your Bluetooth device when not in use.
Financial Data: consider isolating your financial transactions such as online banking on a single computer that is not used for any other online activities including social media and even e-mail.
Smartphone Security: Because most other devices and appliances on a smart home network are typically accessed through your smartphone, gaining access to your smartphone is the goal of a hacker. Be sure to password-protect your smartphone using a password of letters, symbols and numbers. Better still, if your phone offers fingerprint access, strongly consider it.
App Purchases: Not all apps are created to be safe. Your best chance to get safe apps is to purchase them through verified app stores such as Google where the apps are tested for flaws and malicious code. Downloading apps from an unverified third party or without knowing that the app’s privacy policy shows how your information will be handled could allow access for hackers.
Smart Device Purchase: When you purchase a new smart device for your home network, be sure that it is still in its original packaging to avoid tampering. Hackers have been known to purchase a device, infect it with malicious code, return it to the retailer and then wait for an unassuming shopper to purchase and install it.
Safely Disposing of Smart Devices: If you are getting rid of a smart device, be sure to remove any data and reset back to factory default settings to prevent someone else from gaining access to your network through the device later.
In short, be aware and be prepared. Know that, when you deploy smart technology, there are risks. Regard your smart devices the same as you would your phone or computer.
Homeowners Insurance Tip
Take the time to contact your insurance agent to check your homeowners and identity theft coverage before you find you need it. You could find that your coverage includes assistance in identity recovery and/or other forensic expert assistance in the event you do suffer a breach.
Feel free to contact any of our very capable and experienced agents at the William M. Sparks Insurance Agency here in Lutherville/Timonium MD to discuss your home insurance. We can help you review your current insurance policy and explore your options to be sure you have the best coverage and protection according to your circumstances.


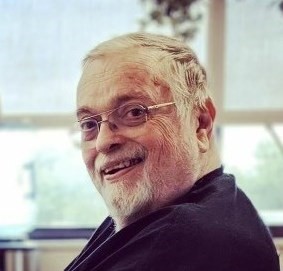 William M. Sparks 1945 - 2023
William M. Sparks 1945 - 2023


